
Researchers revealed an ongoing crypto mining campaign has upgraded its arsenal while adding new defense evasion tactics that enable the threat actors to conceal the intrusions and fly under the radar.
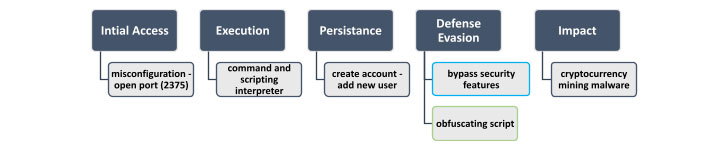
Initial attacks involved executing a malicious command upon running a vanilla image named “alpine:latest” that resulted in the download of a shell script named “autom.sh. Adversaries commonly use vanilla images along with malicious commands to perform their attacks.
The shell script initiates the attack sequence, enabling the adversary to create a new user account under the name “akay” and upgrade its privileges to a root user, using which arbitrary commands are run on the compromised machine with the goal of mining cryptocurrency.
Its new ability is to disable security mechanisms and retrieve an obfuscated mining shell script that was Base64 encoded five times to get around security tools.
Malware campaigns carried out to hijack computers to mine cryptocurrencies have been dominated by multiple threat actors such as Kinsing, which has been found scanning the internet for misconfigured Docker servers to break into the unprotected hosts and install a previously undocumented coin miner strain.
TeamTNT group has been striking unsecured Redis database servers, Alibaba Elastic Computing Service instances, exposed Docker APIs, and vulnerable Kubernetes clusters in order to execute malicious code with root privileges on the targeted hosts as well as deploy cryptocurrency mining payloads and credential stealers.
Miners are a low-risk way for cybercriminals to turn a vulnerability into digital cash, with the greatest risk to their cash flow being competing miners discovering the same vulnerable servers, it uses PowerShell script to disable malware protection, execute a miner payload, and harvest Windows credentials.
The particular illustrates that attackers are becoming more sophisticated, continually improving their techniques and their ability to avoid detection by security solutions. To protect against these threats, it’s recommended to monitor suspicious container activity, perform dynamic image analysis, and routinely scan the environments for misconfiguration issues.


