
Researchers uncovered 11 malicious Python packages that have been cumulatively downloaded more than 41,000 times from the Python Package Index (PyPI) repository, and could be exploited to steal Discord access tokens, passwords, and even stage dependency confusion attacks.
The Python packages have since been removed from the repository following responsible of disclosure
- importantpackage / important-package
- pptest
- ipboards
- owlmoon
- DiscordSafety
- trrfab
- 10Cent10 / 10Cent11
- yandex-yt
- yiffparty
- Two of the packages “importantpackage,” “10Cent10,” and their variants were found obtaining a reverse shell on the compromised machine, giving the attacker full control over an infected machine.
- Two other packages “ipboards” and “trrfab” masqueraded as legitimate dependencies designed to be automatically imported by taking advantage of a dependency confusion or namespace confusion.
Once malicious actor deliberately publishes packages with misspelled names of popular variants, dependency confusion works by uploading poisoned components with names that are the same as the legitimate ones to public repositories, but with a higher version, effectively forcing the target’s package manager to download and install the malicious module.
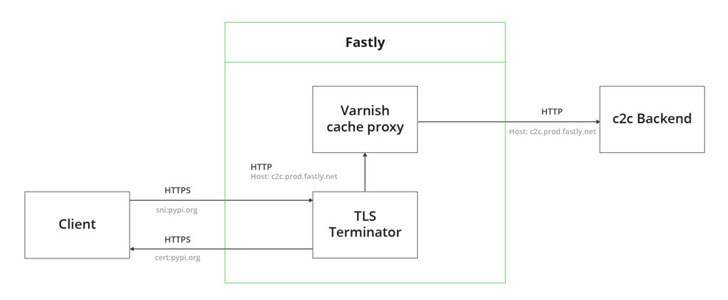
The dependency “importantpackage” also stands out for its novel exfiltration mechanism to evade network-based detection, which involves using CDN to mask its communications with the attacker controlled server as communication with pypi[.]org sending a HTTP request later same redirected to CDN.
Packages “ipboards” and a fifth package named “pptest” were discovered using DNS tunneling as a data exfiltration method by relying on DNS requests as a channel for communication between the victim machine and the remote server.
Efforts to target popular code registries like Node Package Manager JavaScript registry, PyPI, and RubyGems have become commonplace and a new frontier for an array of attacks.
Atleast three NPM developer accounts were compromised by bad actors to insert malicious code into popular packages “ua-parser-js,” “coa,””rc,” GitHub earlier this week outlined plans to tighten the security of the NPM registry by requiring MFA for maintainers and admins starting in the first quarter of 2022.
The development also comes as the software development and version control platform disclosed that it addressed multiple flaws in the NPM registry that could have leaked the names of private packages and allowed attackers to bypass authentication and publish versions of any package without requiring any authorization.




