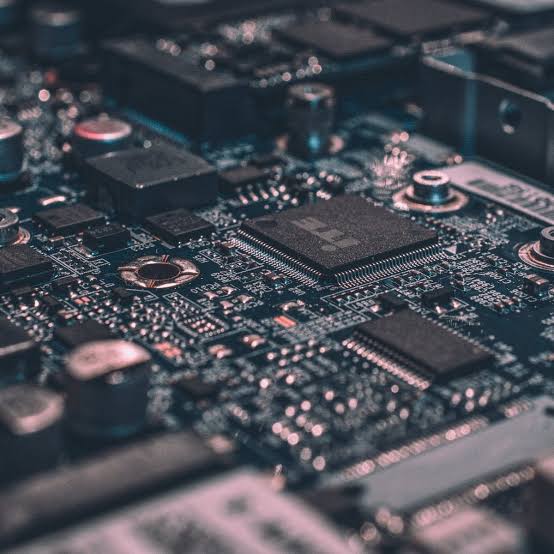
MITRE and CISA have announced the release of the 2021 CWE Most Important Hardware Weaknesses list.
The list was published with the intent of raising awareness of common hardware weaknesses through CWE and educating designers and programmers on how to address them as part of the product development lifecycle.
The list includes a total of 12 vulnerabilities entries that had a score from 1.03 to 1.42 (the highest possible score was 2.0). Below is the list of weaknesses shared by the two organizations order by CWE identifier:
- CWE-1189-Improper Isolation of Shared Resources on System-on-a-Chip (SoC)
- CWE-1191-On-Chip Debug and Test Interface With Improper Access Control
- CWE-1231-Improper Prevention of Lock Bit Modification
- CWE-1233-Security-Sensitive Hardware Controls with Missing Lock Bit Protection
- CWE-1240-Use of a Cryptographic Primitive with a Risky Implementation
- CWE-1244-Internal Asset Exposed to Unsafe Debug Access Level or State
- CWE-1256-Improper Restriction of Software Interfaces to Hardware Features
- CWE-1260-Improper Handling of Overlap Between Protected Memory Ranges
- CWE-1272-Sensitive Information Uncleared Before Debug/Power State Transition
- CWE-1274 -Improper Access Control for Volatile Memory Containing Boot Code
- CWE-1277-Firmware Not Updatable
- CWE-1300-Improper Protection of Physical Side Channels
The experts also shared a list of additional five weaknesses, included in the Hardware Weaknesses, that should be addressed by risk managers.
- CWE-226-Sensitive Information in Resource Not Removed Before Reuse
- CWE-1247-Improper Protection Against Voltage and Clock Glitches
- CWE-1262-Improper Access Control for Register Interface
- CWE-1331-Improper Isolation of Shared Resources in Network On Chip (NoC)
- CWE-1332-Improper Handling of Faults that Lead to Instruction Skips
The 2021 CW Most Important Hardware Weaknesses is the first of its kind and the result of collaboration within the Hardware CWE Special Interest Group, a community forum for individuals representing organizations within hardware design, manufacturing, research, and security domains, as well as academia and government.
Security analysts and test engineers can use the list in preparing plans for security testing and evaluation. Hardware consumers could use the list to help them to ask for more secure hardware products from their suppliers. This list can be used as a measuring stick of progress in their efforts to secure their hardware and ascertain where to direct resources to develop security tools or automation processes that mitigate a wide class of vulnerabilities by eliminating the underling root cause.


