Phishing campaigns that distribute weaponized Microsoft Office documents to prompt victims to enable macros in order to trigger the infection chain directly, new findings indicate attackers are using non-malicious documents to disable security warnings prior to executing macro code to infect victims’ computers.
The malware a descendant of the infamous ZeuS banking trojan is well known for aggressively using macro-enabled Office documents as an initial attack vector to steal credentials and personally identifiable information from users of targeted financial institutions.
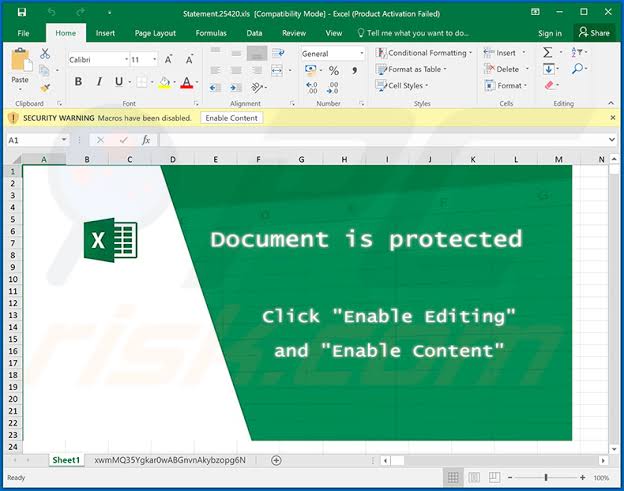
The researchers found that the infection chain started with a phishing email containing a Microsoft Word document attachment that, when opened, downloaded a password-protected Microsoft Excel file from a remote server. However, it’s worth noting that macros need to be enabled in the Word document to trigger the download itself.

After downloading the XLS file, the Word VBA reads the cell contents from XLS and creates a new macro for the same XLS file and writes the cell contents to XLS VBA macros as functions.
Once the macros are written and ready, the Word document sets the policy in the registry to ‘Disable Excel Macro Warning’ and invokes the malicious macro function from the Excel file. The Excel file now downloads the ZLoader payload. The ZLoader payload is then executed using rundll32.exe.
Malicious documents have been an entry point for most malware families and these attacks have been evolving their infection techniques and obfuscation, not just limiting to direct downloads of payload from VBA, but creating agents dynamically to download payloads.
Usage of such agents in the infection chain is not only limited to Word or Excel, but further threats may use other living off the land tools to download its payloads.



